Who to talk to
If you are considering deploying Tines in a self-hosted environment, please first contact your Account Executive or Customer Success Manager to explore your options.
Following that conversation you’ll be put in touch with the right technical resources in Tines to help you access the Tines Docker images, to guide you through the installation and to provide ongoing support.
We highly recommend sharing this page early with your internal IT/infrastructure/network admin/security teams etc. (as appropriate) to provision the infrastructure, services and network connectivity required.
Compatible environments
Tines self-hosted artifacts are delivered as a set of Docker images, which means it runs in any containerized environment where Docker images can run. Tines has been deployed successfully by our customers in the following environments:
AWS Elastic Container Service (Fargate and EC2)
AWS Elastic Kubernetes Service
Azure Container Service
Azure Kubernetes Service
Google Kubernetes Engine
Red Hat OpenShift
VMware Virtual Machine
Docker Compose on:
AWS EC2 instances
Azure Virtual Machine Instances
Google Virtual Machine Instances
Tines will support our application running on any container orchestration system and infrastructure once the requirements laid out below are satisfied (though correct operation of that container orchestration system and infrastructure remains the responsibility of the customer).
We have detailed guides for installing Tines on a single server via Docker Compose, and in AWS via AWS ECS Fargate. If you do not have an existing container orchestration system, we recommend you start there.
System overview
There are 8 basic system components.
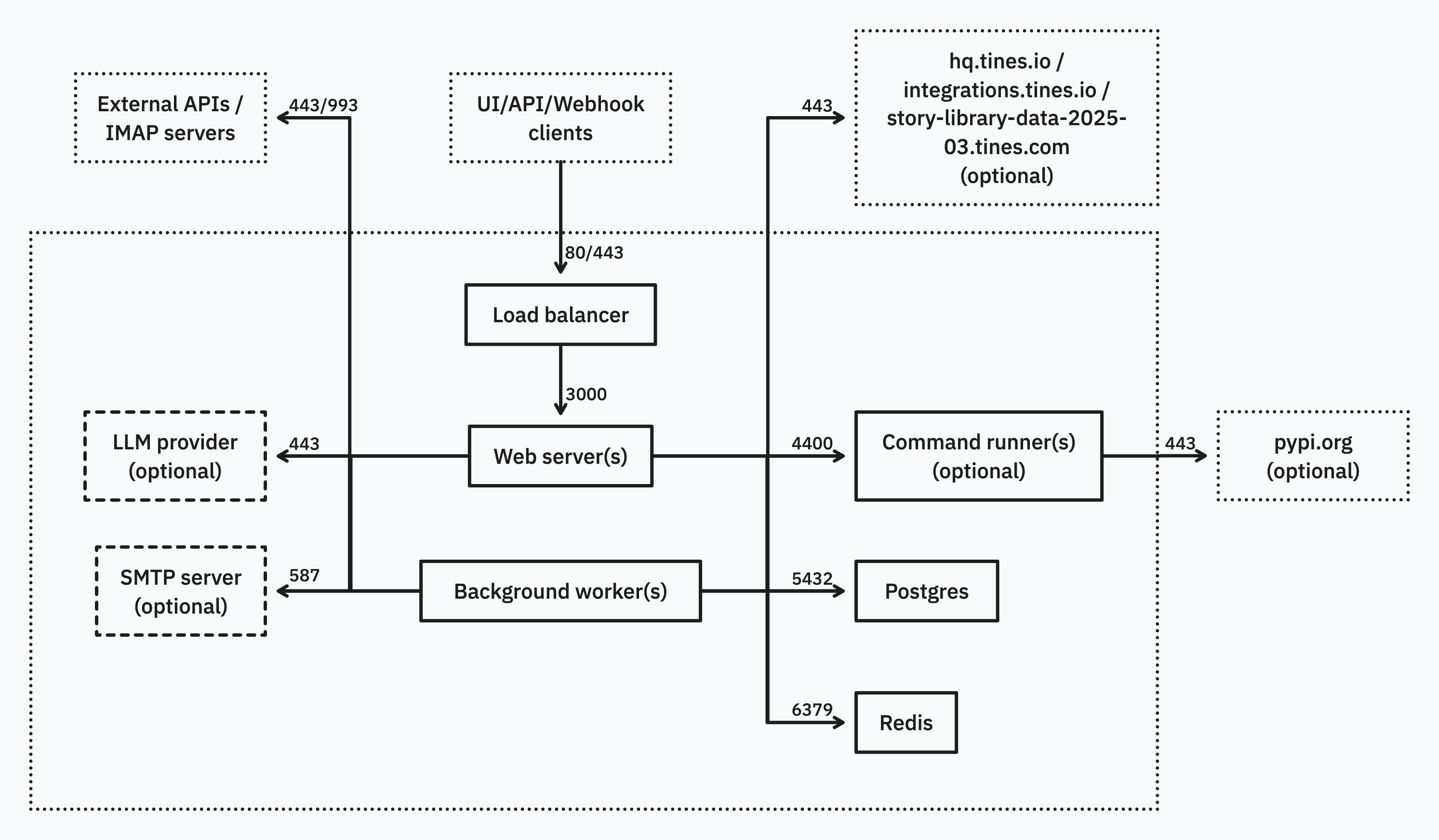
The Web server, Background worker and Command runner (optional) components form the core Tines application and must be run as Docker containers.
The Load balancer, Postgres and Redis components may be run as Docker containers, but where possible we recommend using available dedicated infrastructure.
The SMTP server (optional) and LLM provider (optional) must be provided by the customer.
Connectivity requirements
System requirements
Load balancer
Customers may choose to either use the nginx container we provide or use dedicated load balancing or reverse proxying infrastructure (e.g. AWS ALB) to route traffic to the web server component.
💡Note
Web server
Background worker
💡Note
Command runner (optional)
💡Note
Postgres
Tines uses Postgres 14.x as its persistent data store. Customers may choose to either use the official postgres Docker image and run it as a container or use dedicated infrastructure (e.g. AWS RDS) to host a Postgres database. We highly recommend using a hosted service where possible to simplify scaling and backups etc.
Redis
Tines uses Redis 6.x as its cache, in-memory datastore and queuing mechanism. Customers may choose to either use the official Redis Docker image and run it as a container or use dedicated infrastructure (e.g. AWS ElastiCache) to host a Redis instance. We highly recommend using a hosted service where possible to simplify scaling etc.
SMTP server (optional)
Tines can be connected to customer provided SMTP server to send emails related to user management, monitoring, notifications and to power the Send Email action.
LLM provider (optional)
As described in our AI documentation on providers, Tines can be connected to a number of different AI providers. Configuring this is required to enable all AI features.