⚠️Warning
In 2019, Security and IT organizations are finding it harder to source and retain talent, which is why many companies are embracing remote workers and distributed teams. Communicating within and between remote teams is challenging, and many organizations are using communication tools like Slack and Microsoft Teams, and with them, chatbots, to improve communication and collaboration.
Often during a security incident, security teams create virtual rooms to discuss the details, investigate IOCs, and take action. Frequently, multiple teams from different disciplines are invited. On IT and Product Development teams, virtual rooms are often created on a per-project basis to discuss project-specific initiatives and challenges.
This process of collaborating within a chat tool is commonly called “ChatOps” – “a collaboration model that connects people, tools, process, and automation into a transparent workflow” according to Atlassian.
ChatOps can be improved significantly using chatbots – autonomous programs that interact with users within chats. They provide the “automation” part of ChatOps and allow users to take actions from within their chat application. ChatOps and chatbots allow analysts to maintain their focus in one location, and to operate using just one pane of glass – keeping them focused on performing more meaningful and impactful work.
In order for ChatOps to be successful, it requires both the ability to kick off automated actions from within the chat application and an automation solution to send alerts and data back to the chat program either proactively or reactively.
Because most security and IT tools don’t integrate natively with Slack or Microsoft Teams, you can use Tines to connect your tools together by creating a Tines chatbot. These chatbots can leverage the full power of the Tines Automation platform and send data back to Microsoft Teams or Slack.
The idea of chatbots for security and IT teams is not new – security teams in Slack, Netflix and Dropbox, among others, have created open-source chatbots for alerting purposes and for indicator enrichment. Creating your own chatbot which fits your own internal processes allows you to be more flexible in your tool and process choice, and keeps your information private, however you should check out their blogs for useful ideas!
Chatbots blog series
This series will examine:
Setting up chatbots within Microsoft Teams which receives commands from users
Using this chatbot to proactively notify and crowdsource information from users within Microsoft Teams
Setting up chatbots within Slack which can both take commands and crowdsource information from users
This blog will look at the steps required to set up both a communication bot that receives questions and a proactive notification bot, using Tines and Slack, and Microsoft Teams.
At the end of this first tutorial, you will have created a bot that can receive a command to analyze a domain from any user on your team, and respond with the VirusTotal and URLHaus analysis of that domain.
Microsoft Teams communication bot
This first tutorial will examine how to set up chatbots within Microsoft Teams which receives commands from users and replies. Before we begin, you’ll need to be, or be working with, an admin on your Microsoft account. You can also read the getting started with Bots guide, here.
Creating an application in Microsoft Teams
First, let’s begin by Installing App Studio for Microsoft Teams https://aka.ms/InstallTeamsAppStudio
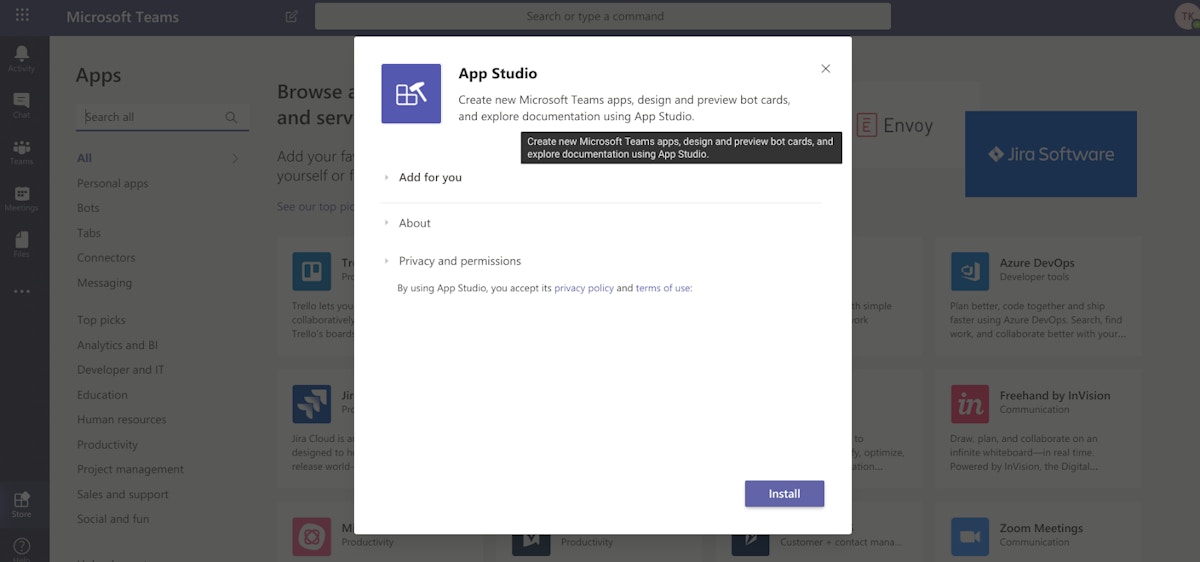
Select Install. When the installation is complete you should get the following notification:
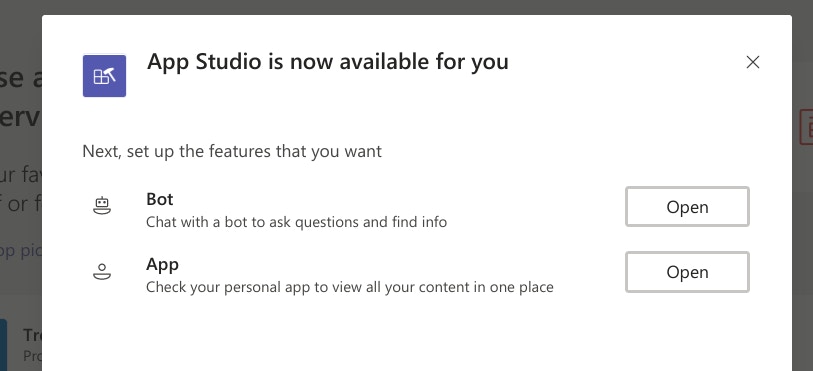
Now click “Open” on setting up a bot within App Studio.
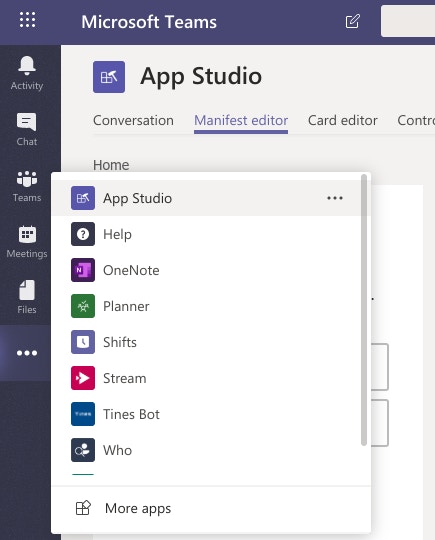
You can also get to this page by clicking the “more” button ( … ) on the sidebar of teams and selecting App Studio
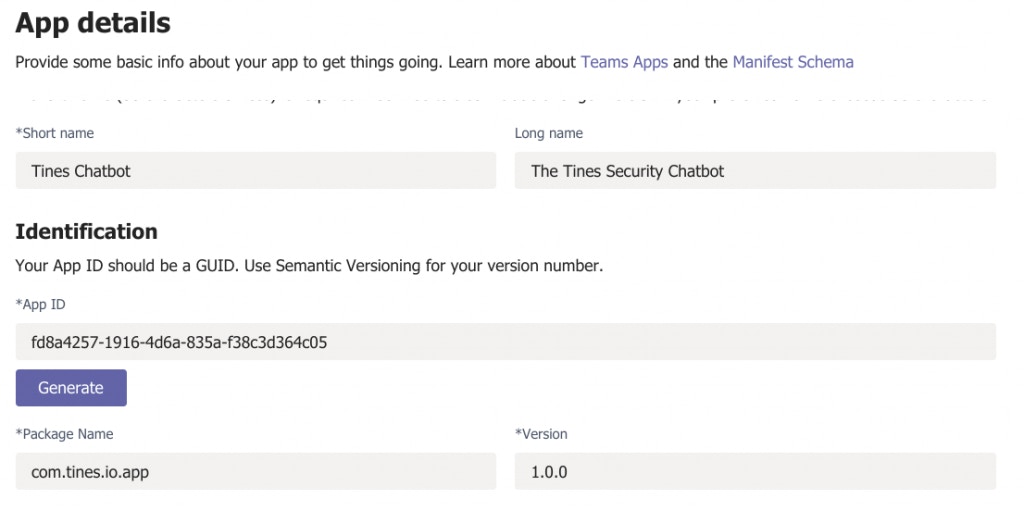
Give your application a name (e.g. the Security chatbot) and a GUID and version number. (Note, this is the application ID, not the Bot ID which is used later on.)
Give your application a description:
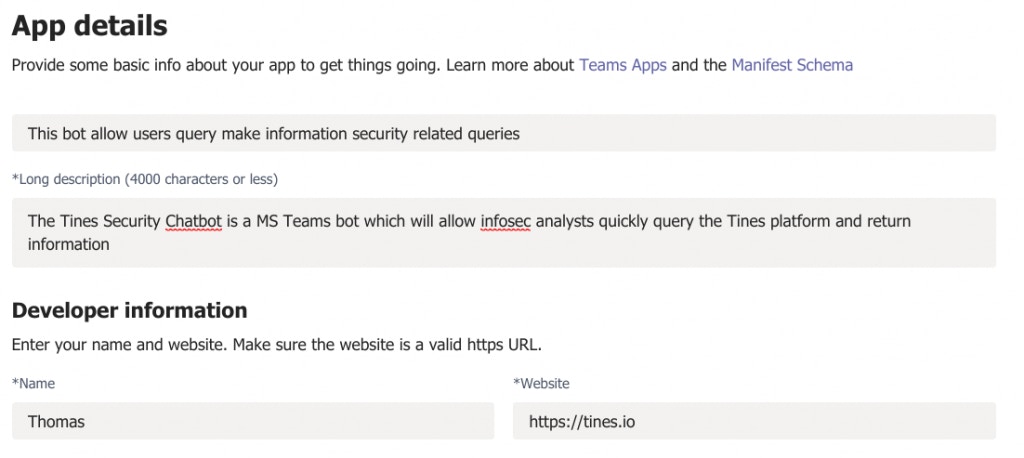
Then enter the Privacy Statement URL, Terms of Use URL, and some branding for your application.
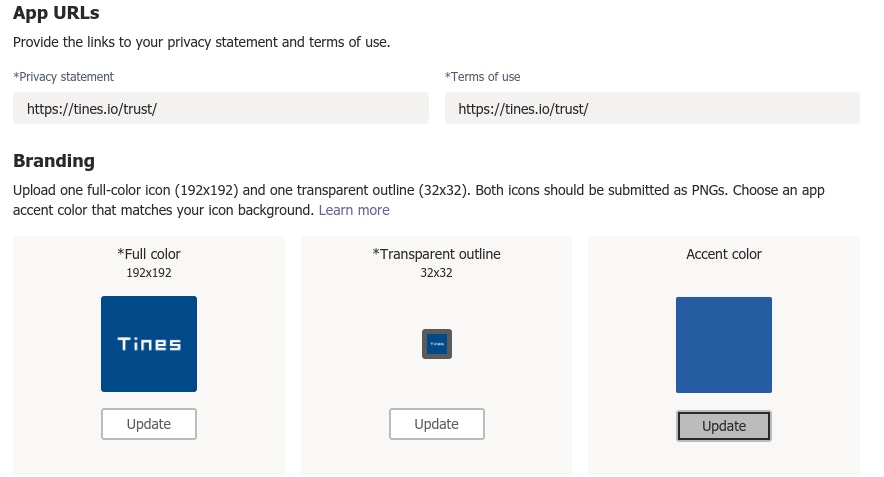
Creating a chatbot for your application
Now go to the Bots tab on the left-hand side of the page:
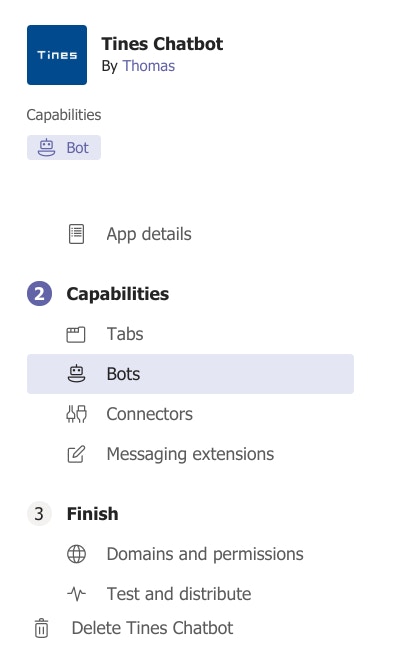
Create a Bot and give it the scopes “Personal”, “Team” and “Group Chat.”
You should also save the ID of the Tines chatbot, just above this.
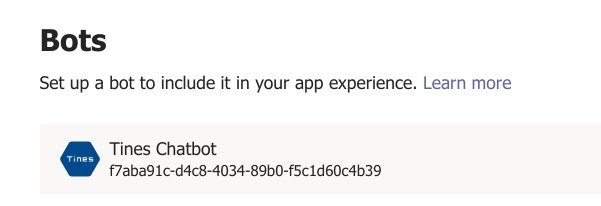
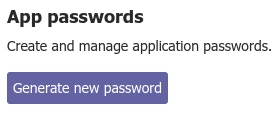
Once you have created your chatbot, click “Generate new password” and keep this safe! This will be used to retrieve your bearer token later.
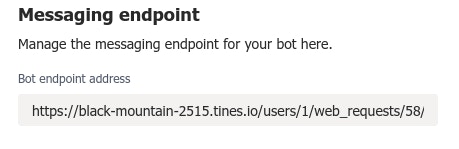
Now, let’s go to Tines and create a webhook using the Webhook template. Let’s call it “receive commands.”
Copy the webhook URL and enter it in the “Bot Messaging Endpoint” path.
Lastly, let’s add a command to “analyzedomain.”
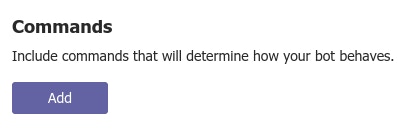
Click “Add Command.”
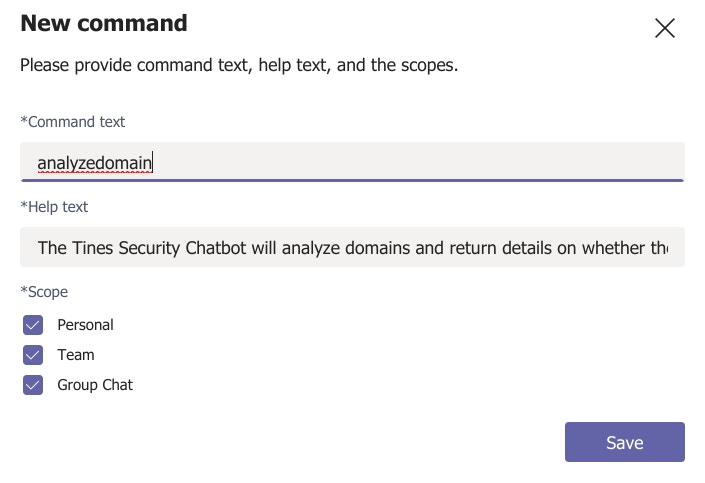
Fill out the details of the command text and help text. Choose the scopes “Personal”, “Team” and “Group Chat.”
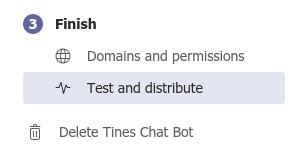
Now, return to the menu and click “Finish > Test & Distribute.”
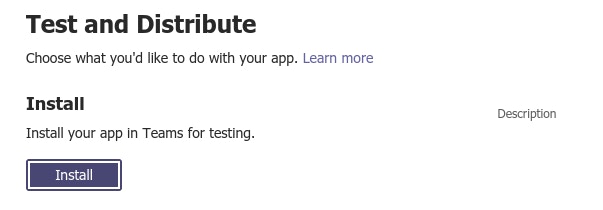
Then click “Install.”
Click “Add for You”, and select the relevant team to add the application for your team.
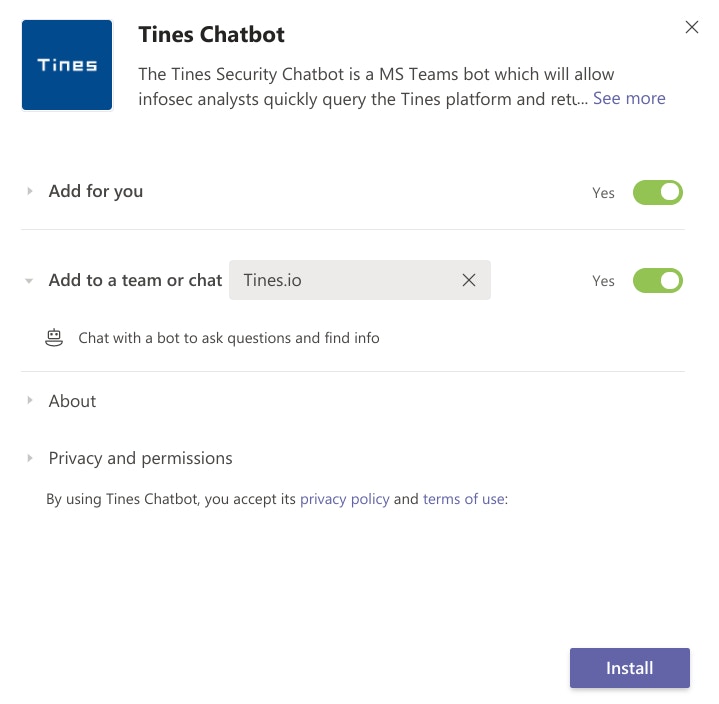
Then click “Install” again.
If you get an error saying “uploading of custom apps is not allowed, then follow the process here. You’ll need to allow sideloading of external apps.
Receiving data in Tines
Congratulations! You’ve just installed a Tines chatbot!
Now, within your team chat, you should be able to call the “Tines chatbot.”
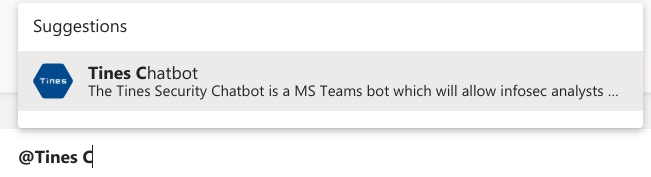
When you “@” the Tines chatbot you’ll be prompted with the command “analyzedomain” or the command we selected earlier.
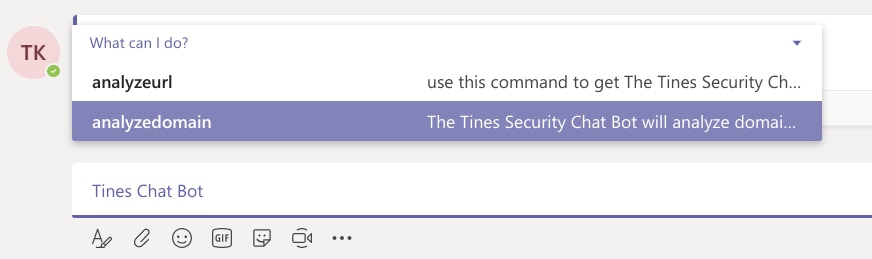
Let’s go ahead and enter the domain “tines.com” and click enter.
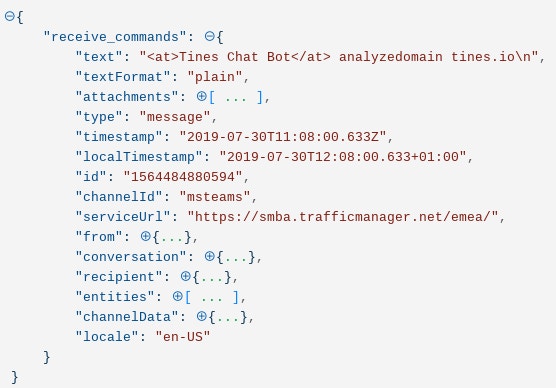
This data will now have been sent by Microsoft Teams to Tines. Check your Webhook Action to make sure data has been sent and received:
If you do not see any data within Tines, make sure the webhook URL specified in the “Bot Messaging Endpoint” above is correct. You should also check that Microsoft Teams is able to reach that webhook (i.e. that it’s not blocked by your Firewall). If you change the webhook address you will need to re-install the application following the instructions above.
Sending a reply to Microsoft Teams
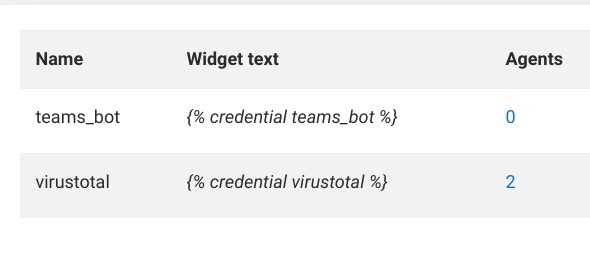
To reply, let’s take the password you saved earlier and save it as a credential in Tines:
Now, let’s examine more closely the data that Tines receives in the Webhook Action.
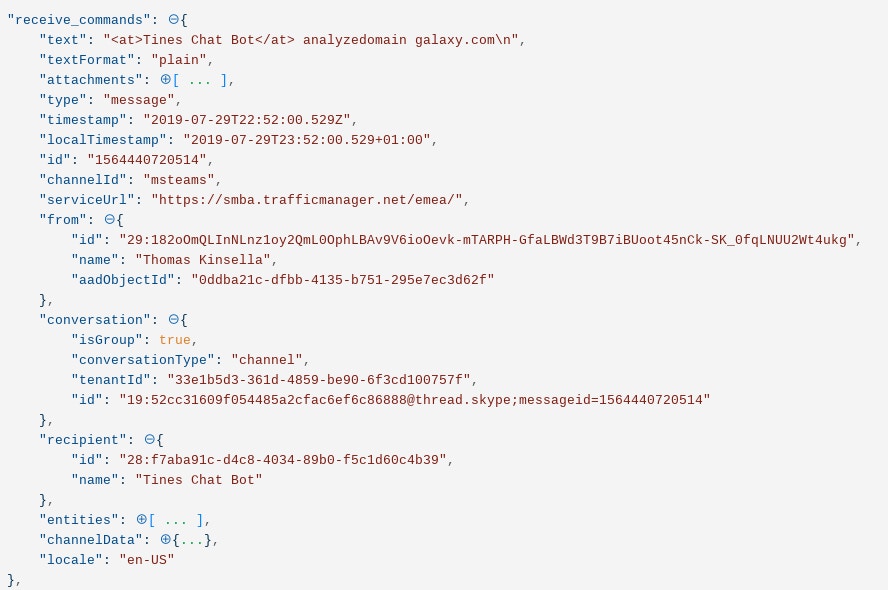
Tines has received the text of the query (analyzedomain galaxy.com). But Tines has also received several other pieces of information we need to reply:
The serviceurl is the base URL that Tines must send data back to using an HTTP Request Action
The “from” details tell Tines who to send this reply to
The recipient id is the recipient ID (note, not the Bot ID) of the Tines bot – this is needed to send the reply as the Tines bot
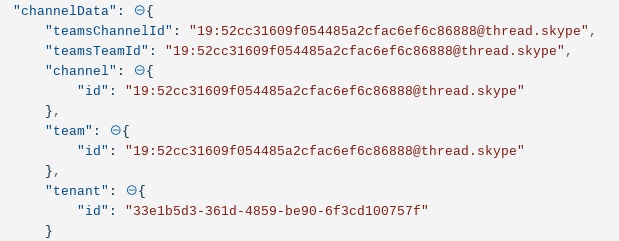
Lastly, Tines has received the channelData – this is important for Part 2 when we enumerate all the members of a channel or team.
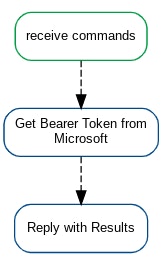
Our first step is to take the password and Bot ID we saved earlier and request a Bearer Token from Microsoft which we can use to reply. Use the below template to request this token.
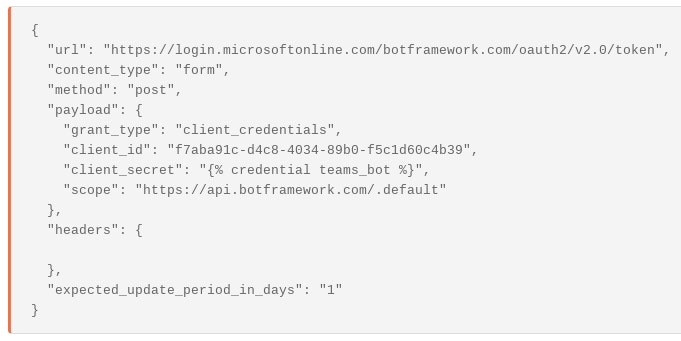
We use the bearer token as a credential in the reply.
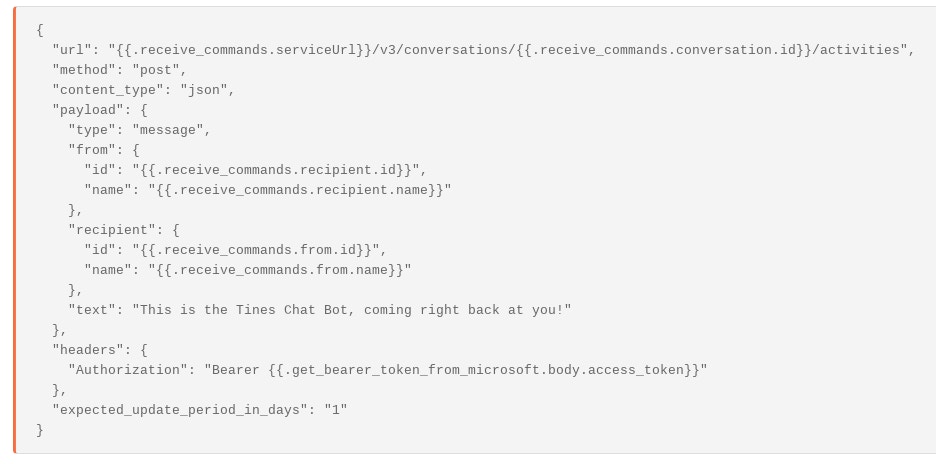
The reply uses the Service URL, the Conversation ID, and sends the data back to the recipient who sent the message, from the Tines chatbot.
Chaining these results together we can reply to every message sent by a webhook:
Congratulations! You’ve just sent a reply! You can download this basic Story here.
Advanced replies
Of course, the aim of this Story is to analyze the domain in VirusTotal, URLHaus, and other services and then reply with the results. In Tines, this is pretty easy to do – just use your own tools or templates to perform the analysis and return the details to the requestor. The example below uses VirusTotal and URLHaus.
The first step of this process is to Trigger on the command being used (in this case, analyzedomain):
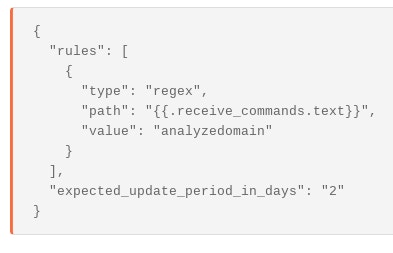
We can create separate flows for each command as we expand the functionality of the Tines chatbot.
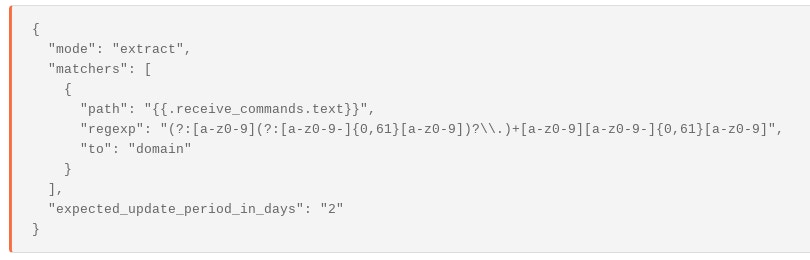
We then extract into an array all the domains in the text.
Tines can then query these domains in VirusTotal and URLhaus, among others.
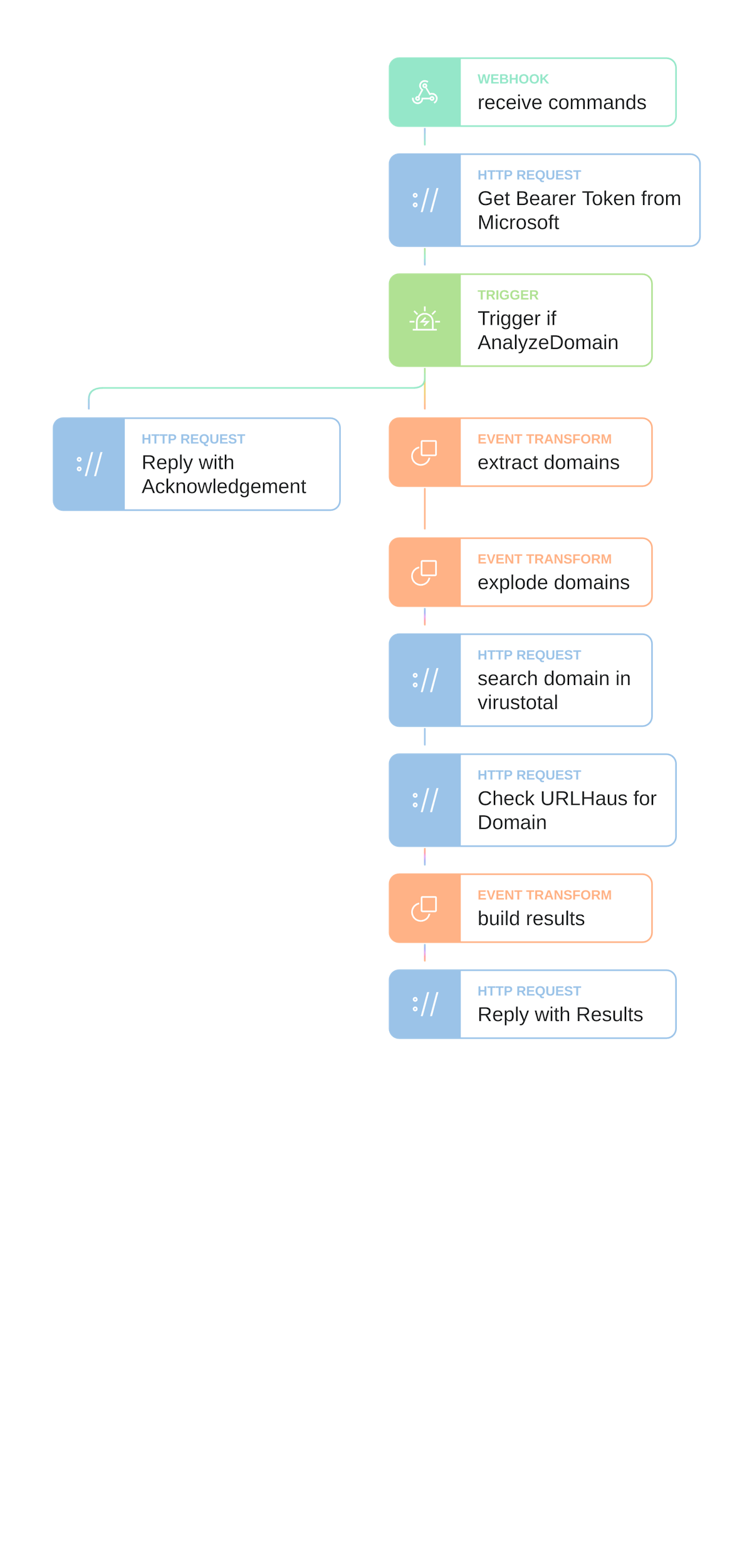
A complete flow will look like the following:
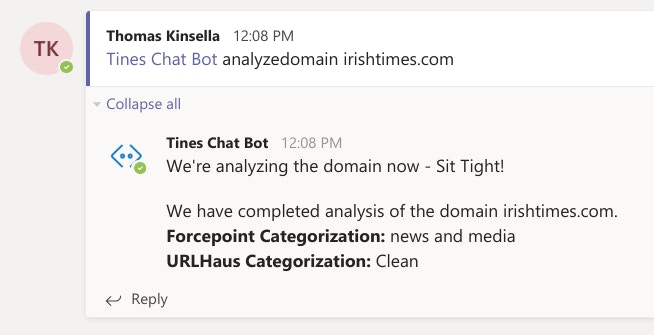
This Story will reply with simple results to the user like the following:
You can download this complete Story here.
Additional use cases
Now, that we have a process to receive data from Microsoft Teams and reply, there are near unlimited possibilities of what we can automate within Tines. Other automation steps you can use with the Tines chatbot include:
Enrich Domains, IPs, URLs
Retrieve User Profile Information from Workday, MSGraph, etc.
Escalate Tickets to On Call
Create Tickets, Subtickets, or Increase Ticket Severity
Add Comments to Tickets
Block Domains and IP addresses
Query Logs
Kick Off Vulnerability Scans and PenTests
Isolate Hosts or Lock User Accounts
Send Push Notifications to other users
Post all updates for an incident in a team room
Post all comments from an incident room to an incident ticket
Sharing Incident Handover Notes
Proactively run any automation Story
Next Up: Part 2 – How to Proactively Send Notifications in Microsoft Teams
*Please note we recently updated our terminology. Our "agents" are now known as "Actions," but some visuals might not reflect this.*