Security teams must defend their organizations against both known and unknown threats. With attackers continually targeting existing security tooling, being able to unlock automated research-grade insights across your data allows you to identify threats and their variants that may have evaded detection elsewhere in your technology stack.
Tines' no-code automation platform allows anyone to build or manage complex security workflows without writing a single line of code. Tines' unique approach to automation enables security teams to connect/integrate well-beyond disparate tools. By combining Tines with the Stairwell Inception platform, organizations have efficient access to automated threat detection and analysis that improves their defenses across systems and workflows.
Inception is a SaaS-based security platform that collects files automatically from an organization and securely stores them in a virtual evidence locker. Once stored, Inception runs every file, from known DLLs from Microsoft to emerging variants of malware, through the same research-grade analysis. This analysis includes YARA intelligence, both Stairwell-authored and your own custom rules, AV scanning, variant discovery, and static and dynamic analysis.
How Inception and Tines work together
Tines extends Stairwell Inception threat intelligence into any system, enabling teams to do more with their insights and enrich their alerts for faster, smarter decision-making. While file enrichment tools have existed for years, with Stairwell Inception, security teams can now revisit the evidence in their environment as new intelligence becomes available to discover what was previously unknown.
Tines and Inception sample use case: SentinelOne
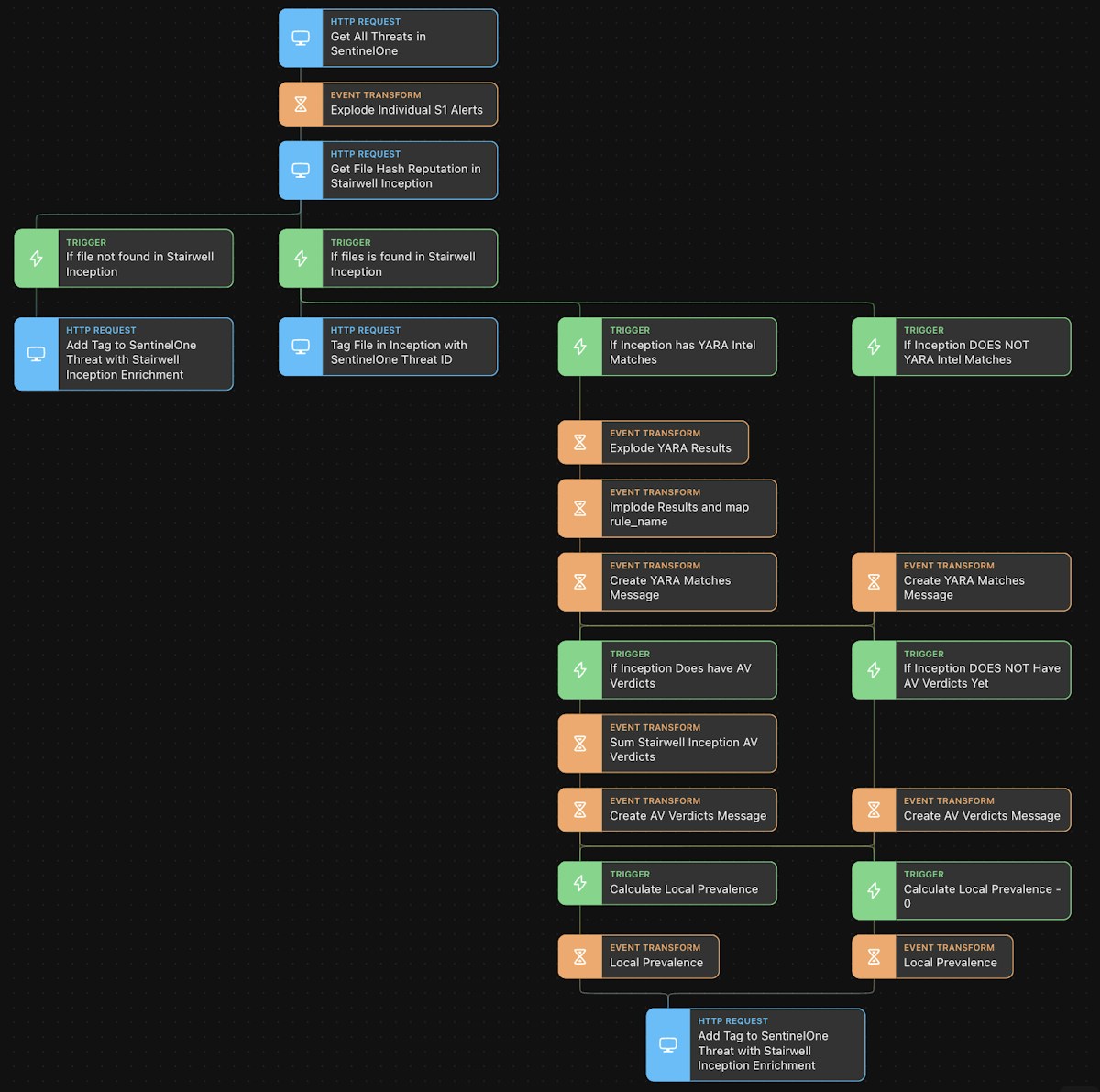
A Tines Story depicting the workflow with Inception triggered by a SentinelOne alert
In this example, Tines retrieves threats from SentinelOne’s threat API and feeds them to Inception. The same outcomes could be achieved with any other endpoint security tool. Once Inception receives the list of active threats, it enumerates each threat and polls its data vault for enrichment. The Inception platform’s capabilities are continually expanding. Today, this enrichment includes:
Variant discovery - Inception identifies variants of known or suspected malware in seconds to speed up your team’s detection and response capabilities
YARA matches - The YARA intelligence can be rules developed and/or aggregated by Stairwell, by an MSSP partner, or custom intelligence authored by a customer
AV verdicts - With 20+ AV engines running privately within the Inception platform, teams get visibility to known threats with signatures
Local prevalence - With Inception file forwarders running within an organization, security teams can get context as to the prevalence of files over time
Inception delivers all of this context automatically for every threat, with the Tines connection, it is visible in the SentinelOne console. This connection also brings SentinelOne threat data to the objects seen within Inception, providing teams with additional context no matter which consoles they are actively using.
Getting started with Tines & Stairwell Inception
With automated research-grade analysis powered by Inception and Tines, security teams are armed with unique threat knowledge that enables them to better and more efficiently protect their organizations. Through this connection, actionable knowledge can be brought to every alert, and automated response can be provided using existing endpoint security tools.
To get started, visit the Tines Story Library to import, use or customize this example workflow in your own Tines tenant. Tines also offers a free, full-featured Community Edition available here. Contact Stairwell here to learn more and try the Inception platform for yourself.
Loading story...