As a tenant owner, it's important to keep track of who's accessing your Tines environment and when. Sign-in activity logs give you visibility into user access patterns, helping you identify potential security issues, audit compliance, and understand how your team is using Tines.
View sign-in activity for users
Tines tracks every time a user signs into the tenant, recording details like the timestamp, IP address, and user agent (browser and device information). You can view this information for individual users or across your entire tenant.
To view sign-in activity for a specific user:
Navigate to the tenant Settings via the team menu.
Navigate to the Users tab.
Select the desired user.
Look for the Last seen timestamp in their profile.
For more detailed sign-in history, you can access the full activity via the See activity button on the user profile. This will redirect you to the Audit logs filtered by the user’s ID.
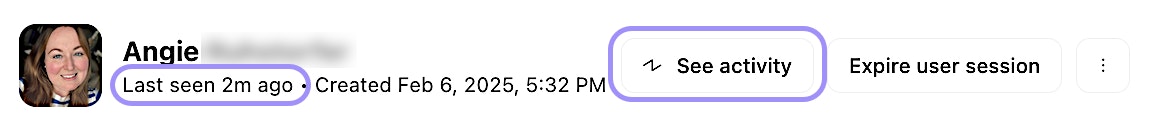
UI location to view a user's activity.
Download sign-in activity logs
For deeper analysis or compliance reporting, you can download sign-in activity logs in CSV format. This allows you to import the data into spreadsheet tools, SIEM platforms, or other analysis systems.
The CSV file includes:
User email
Sign-in timestamp
IP address
User agent (browser and device information)
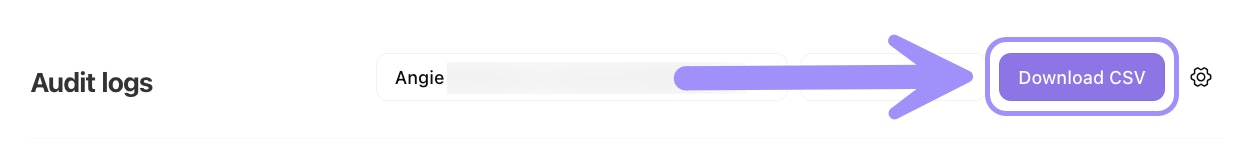
UI location to export Audit logs in CSV format.
Sign-in metadata
Each sign-in event captures three key pieces of metadata:
Timestamp: The exact date and time the user signed in. This is recorded in your tenant's time zone.
IP address: The public IP address from which the user accessed Tines. This can help you identify the user's location or network.
User agent: A string that identifies the browser and device the user was using. For example, you might see "Chrome on Windows" or "Safari on iPhone."
Monitor user access patterns
Beyond just viewing individual sign-in events, you can use sign-in activity data to identify patterns and trends. Here are a few things to look for:
Unusual sign-in times: If a user who typically signs in during business hours suddenly has activity at 3 AM, it could indicate a compromised account.
Unfamiliar IP addresses: If a user signs in from an IP address in a different country or region than usual, it might warrant investigation.
Inactive users: If a user hasn't signed in for several months, you might consider removing them from the tenant or adjusting their permissions.
High activity users: Identifying your most active users can help you understand who's driving workflow adoption in your organization.