Analyze CrowdStrike detections
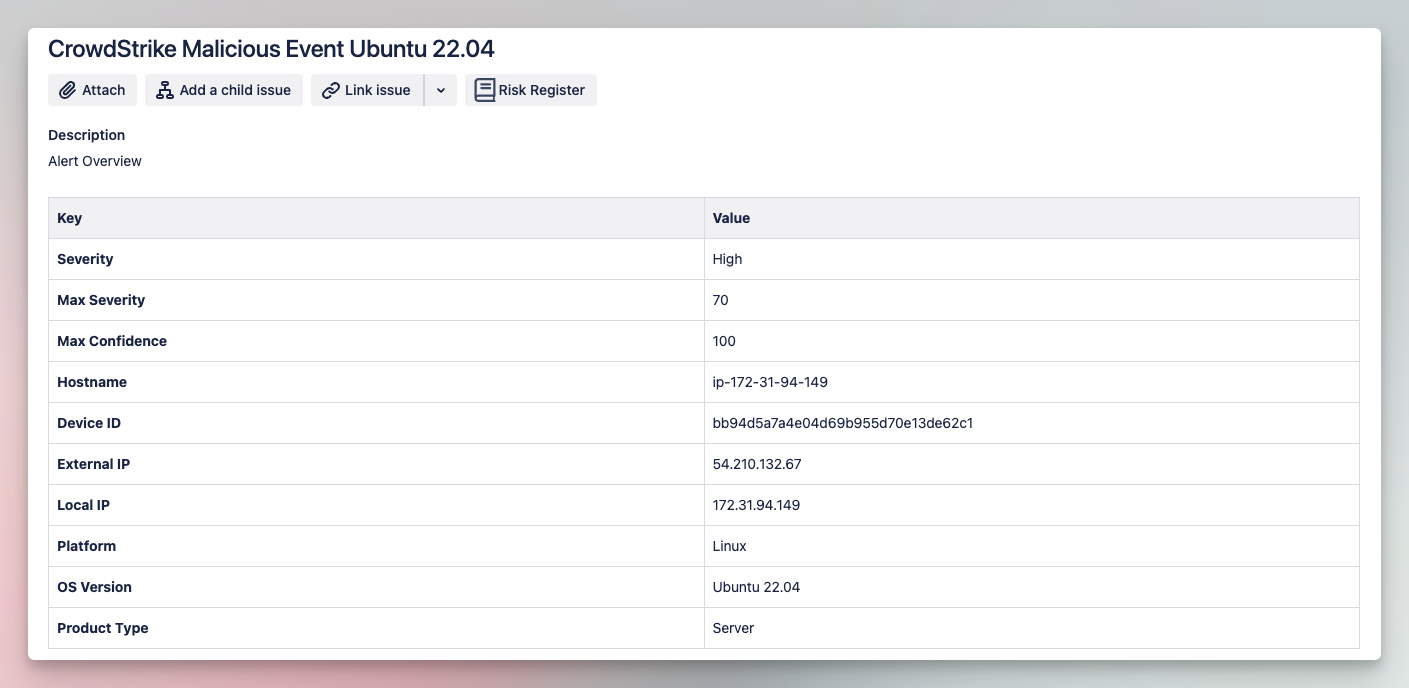
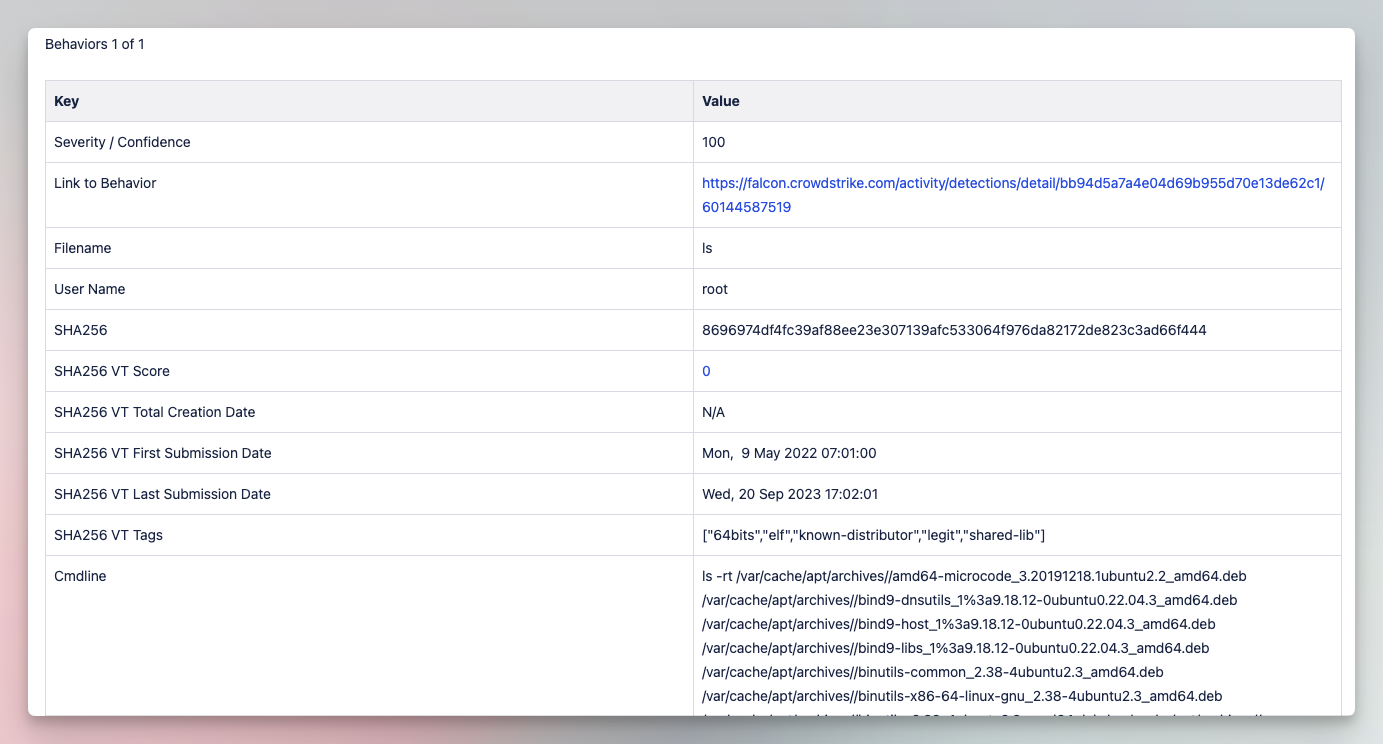
Pulls a list of new CrowdStrike Detections, flags them as in progress in CrowdStrike, and gets the detection details for each one. For each detection, the individual behaviors are examined, and the process hash is checked in VirusTotal to see if it is known malicious. Where there is a provided IOC as part of the behavior, this is also checked in VirusTotal. A Jira ticket is created for each Detection, and a message sent to a Slack Channel.
Tools
How it works
Import this story to your tenant, from where you can adapt it to meet your unique needs.
ImportWas this story helpful?